Are you running your code or malicious code?
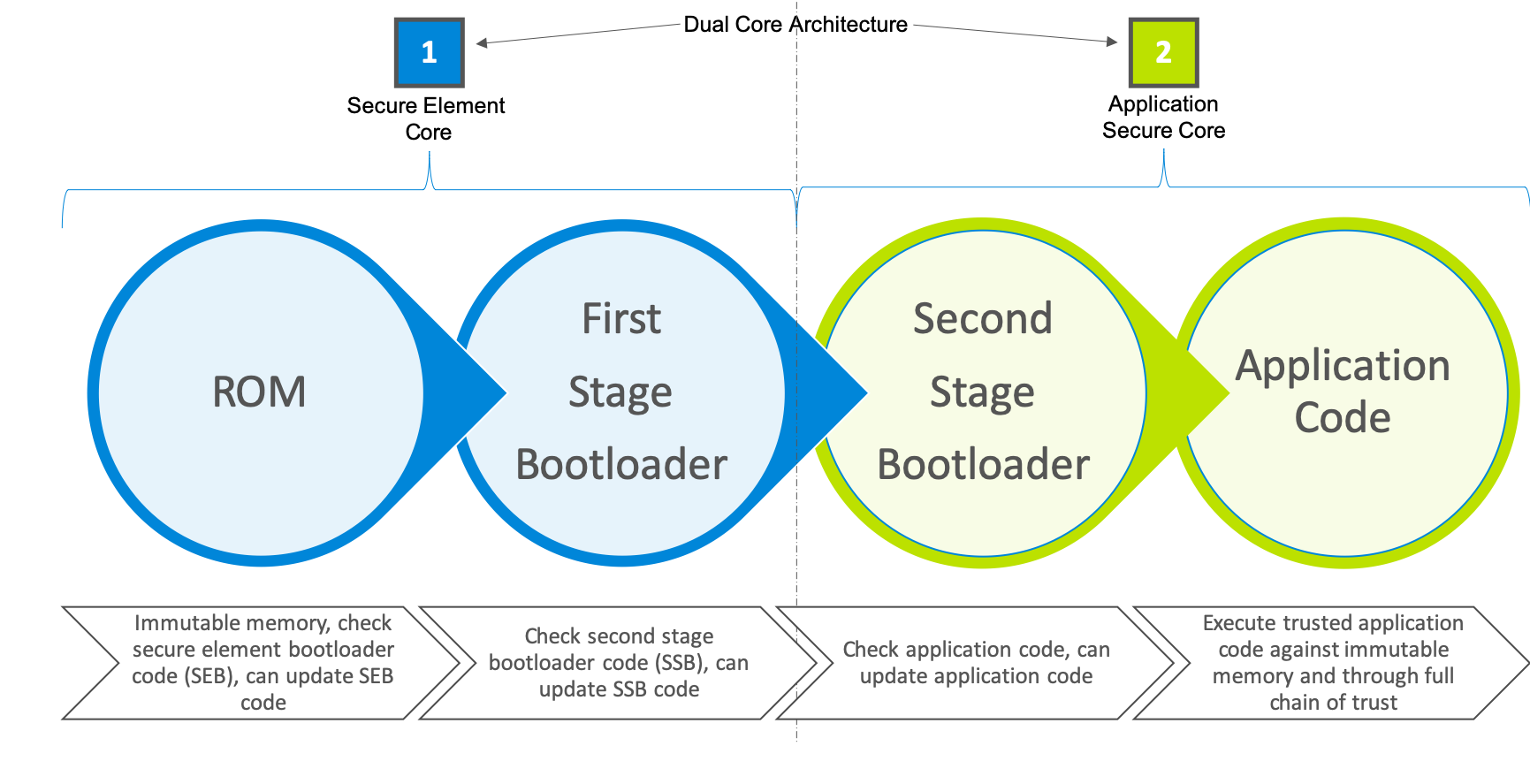
A common implementation of Secure Boot consists of storing the public key used for code authentication into one-time programmable memory. As the public key becomes irreversible, only code signed with the corresponding private key can be authenticated and executed. Silicon Labs enhanced Secure Boot implementation is called Secure Boot with Root of Trust and Secure Loader (RTSL). Secure Boot with RTSL takes additional steps by following a full chain of trust process. With a dual core architecture, the process starts at the secure element. The code starts from secure immutable ROM and confirms authenticity of the first stage bootloader. It is also checks for updates via a secure loader. Once the secure element is fully verified and available, the second core initiates the second stage authentication and updates are applied, if required. In the final stage, the second stage bootloader checks, updates (if applicable) and authenticates the application code.
Have you Discovered a Vulnerability?
Our Product Security Incident Response Team (PSIRT) is responsible for ensuring the vulnerabilities discovered in our products are mitigated and communicated responsibly. If you detect a security threat, let us know.
Information on how to subscribe to security notices can be found here.