-
Product
Product
Industry-Leading Security for Evolving IoT Threats
Securing the IoT is challenging. It’s also mission-critical. The challenge of protecting connected devices against frequently surfacing IoT security vulnerabilities follows device makers throughout the entire product lifecycle. Protecting your product in a connected world is a necessity as customer data and modern online business models are increasingly targets for costly hacks and corporate brand damage. To stay secure, device makers need an underlying security platform in the hardware, software, network, and cloud. We’ve got you covered.
Secure Vault
Secure Vault™ is an industry-leading suite of state-of-the-art security features that address escalating Internet of Things (IoT) threats, greatly reducing the risk of IoT ecosystem security breaches and the compromise of intellectual property or revenue loss from counterfeiting. Specifically, Secure Vault technology:
- Protects against scalable local and remote software attacks
- Defends against local hardware attacks, which – although historically less common than software attacks – are on the rise due to the surge of affordable and easily accessible tools
- Passes testing from independent, third-party laboratories that attempt to infringe security functions for a specified amount of time with sophisticated equipment
What Level of Security is Right for You?
-
High
-
Mid
-
Base
Secure Vault - High
Maximum security of the device is made available by protecting the communication channel and the device itself, both against logical and physical attack vectors. In addition to Vault-Mid capabilities, keys are wrapped using a Physically Unclonable Function (PUF), each device has a private key that uniquely identifies it, and the device also has advanced tamper detection settings that protect the device from any physical form of tamper.
Secure Vault - Mid
High level of security provided by ensuring protection of the communication channel and protection against logical attack vectors. In addition to Vault-Base capabilities, devices have authenticated firmware running on them thanks to a secure booting sequence with a Root of Trust and Secure Loader (RTSL). Devices also have secure debug capabilities to ensure only authentic personnel have the capability to debug the device. Secure Vault-Mid parts also include TrustZone support*. TrustZone support will enable protected storage of keys and other application firmware.
*TrustZone support is currently available on all BLE device, with a plan to release this support to
all other stacks in the near future.
Secure Vault - Base
Good level of security provided on the devices to by protecting the communication channel between two devices and encrypting the data that flows within it. Salient features of this tier include a secure application boot, proven cryptographic engines, and a True Random Number Generator (TRNG) function.
Silicon Labs IoT Product Security
| Feature | Series 3 Secure Vault™ |
High | Mid | Base |
| Security Framework | PSA Certified Level 4 |
PSA Certified Level 3 |
PSA Certified Level 2 |
PSA Certified Level 1 |
| True Random Number Generator | ✔ | ✔ | ✔ | ✔ |
| Crypto Engine | ✔ | ✔ | ✔ | ✔ |
| Secure Application Boot | ✔ | ✔ | ✔ | ✔ |
| Secure Engine | HSE | HSE | VSE/HSE | — |
| TrustZone | ✔ | ✔ | ✔ | — |
| Secure Boot with RTSL | ✔ | ✔ | ✔ | — |
| Secure Debug with Lock/Unlock | ✔ | ✔ | ✔ | — |
| DPA Countermeasures | ✔ | ✔ | Select OPNs | — |
| Anti-Tamper | ✔ | ✔ | — | — |
| DFA Detection | ✔ | — | — | — |
| Authenticated XiP (AXiP) | ✔ | — | — | — |
| Secure Attestation | — | ✔ | — | — |
| Secure Key Management | ✔ | ✔ | — | — |
| Advanced Crypto | ✔ | ✔ | — | — |
Third Party Accreditation
Secure Vault has gathered third party accreditations & validations since its original launch in early 2020.
-
Certifications
Certifications
At Silicon Labs, security is foundational to how we design, build, and deliver wireless technology.
Information security is a top priority and an important component of our day-to-day operations. As the world becomes more connected, every device, network, and ecosystem depends on trust. We follow industry practices, pursue alignment with standards, and embed security at every layer to protect data, devices, and the people who rely on them. With deep engineering expertise, a culture of integrity, and a commitment to continuous improvement, we ensure that innovation and security advance together – so that every connection is both smart and secure.
Click here to learn how we uphold the highest standards through our certified Information Security Management System (ISMS) and company-wide commitment to security.
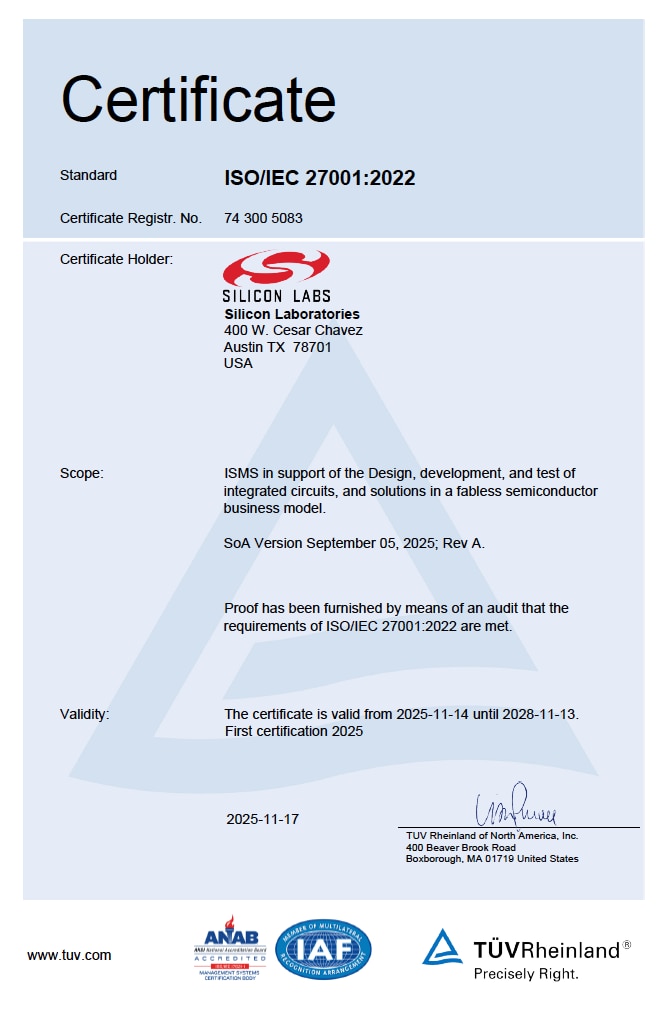
Silicon Labs ISO 27001:2022 Certificate
Our commitment to security is validated by our ISO 27001:2022 certification. This certification confirms that our security practices comply with one of the world's most rigorous international standards for information security managemnet. Siliocn Labs is ISO 27001:2022 certified with TÜV Rheinland of North America.
Commitment to Product Security
As evidenced by the scope of our ISO 27001:2022 certification, product security is at the heart of our innovation. We design, develop, and test our integrated circuits and solutions with security built in from the ground up, across the entire hardware and software lifecycle management. Through our secure development lifecycle practice, continuous testing, coordinated vulnerability disclosure, and trusted supply chain practices, we ensure our products meet the highest standards of resilience and integrity. Our goal is to enable secure, connected devices that protect data, safeguard users, and inspire confidence in every deployment.
Visit our product section to learn more.
For Quality and Environmental certifications visit this page.
-
CRA
CRA
CRA Readiness that is Built on Secure Product Design, Lifecycle Governance, and Coordinated Vulnerability Handling.
Silicon Labs is reviewing and updating our existing products, processes, and supporting documentation to ensure conformance with the European Union Cyber Resilience Act (CRA). Our approach combines secure-by-design development, product security governance, public vulnerability handling, and evidence-backed readiness activities across the product lifecycle.
Our Commitment to the Cyber Resilience Act
The CRA determines horizontal cybersecurity requirements for products with digital elements placed on the EU market. It raises expectations for secure development, vulnerability handling, user information, technical documentation, and lifecycle support.
Silicon Labs will ensure conformance to our applicable CRA obligations for secure product lifecycle controls, documentation, PSIRT operations with coordinated vulnerability handling, and internal practices. These practices have already been in place, based on other security standards, certifications, and/or frameworks.
This page is designed to communicate that readiness while linking visitors to the official regulation text, relevant certification pages, product security resources, and reporting channels.
Why This Matters
Product manufacturers need confidence that their silicon and software suppliers can support secure deployment, vulnerability response, software transparency, and lifecycle maintenance under tightening global regulations.
CRA Milestones
CRA Key Topics
Cyber Risk Assesment
Silicon Labs drives pro-active Risk Assessment activities.
General Requirements
Silicon Labs supports secure end-to-end product design and support.
Information and Instructions to the Users
Silicon Labs provides security guidance to customers.
Technical Documentation
Silicon Labs provides helpful resources.
Reporting Requirements
Silicon Labs provides security vulnerability reports and patches.
See below for more on the CRA Key Topics as well as answers to FAQs.
Silicon Labs Assurance
Alignment with CRA Key Topics
Cyber Risk Assesment
- PSA Certified Level 4: Series 3 Secure Vault establishes a high-assurance hardware root of trust and demonstrates independently validated resistance to sophisticated physical and software attacks. Click here to learn more about this achievement.
- ISO 27001:2022 Certified: Our Information Security Management System supports secure validation and governance across the company, with product security embedded throughout the design, development, and testing processes. View our ISO 27001 Certificate here.
General Requirements
- Secure Design: Hardware Design with security in mind by creating innovative solutions such as Secure Vault™. Software Development that follows industry-recognized secure coding standards and internal guidelines emphasizing code safety
- Vulnerability Management: A centralized system that tracks potential vulnerabilities and ensures prompt triage, remediation, documentation, and a feedback system that strengthens product resilience.
- Continuous Improvement: Security Testing (threat modeling, fuzz testing, regression testing, and periodic penetration assessments) performed throughout the product lifecycle, not just before release.
Information and Instructions to the Users
- Developer Documentation and Answers to Security Vulnerability FAQs: We provide product security resources (powered with AskAI), user guidance, and training resources to help developers implement secure products and maintain them through deployment. Visit our software documentation site, docs.silabs.com and our Security Vulnerability FAQs.
- Training Resources and Developer Enablement: Silicon Labs provides a broad public training ecosystem to help customers implement secure and compliant products, including Tech Talks, Works With on-demand sessions, webinars, and structured curricula across wireless, security, software, and application domains. Click on each link above to learn more.
Technical Documentation
- Technical Documentation for Series 3: The Series 3 wireless platform page connects customers to product information, technical resources, software documentation, hardware documentation, and development tools. We also offer information on SDK Support Policy, SEMS, and Hardware Longevity Commitment, helping support secure implementation and lifecycle adoption for next-generation IoT designs. Learn more about the Series 3 platform.
- SBOM Generation in Simplicity Studio: Simplicity Studio can automatically generate SBOM artifacts in SPDX and CycloneDX formats for supported SLC projects, helping customers manage dependency visibility and software transparency. Learn more about SBOM Generation.
Reporting Requirements
- PSIRT and Vulnerability Disclosure Program: Silicon Labs operates a public vulnerability reporting channel, disclosure policy, and response targets to support coordinated vulnerability handling throughout the product lifecycle. Read our Vulnerability Disclosure Policy.
- CVE Numbering Authority (CNA) with MITRE: Silicon Labs has been a CNA with MITRE since November 2021. To date, only 201 organizations from 32 countries participate in the CVE Program as CNAs. Browse the list of CVEs issued by Silicon Labs. Silicon Labs will be following the security reporting requirements directed by the EU, when its Single Reporting Platform becomes available in September 2026.
- Addressing Security Vulnerabilities: Silicon Labs maintains updates to software including for fixes to security vulnerabilities. See SDK Release and Maintenance Policy for more information.
FAQs
This FAQ addresses practical questions about CRA readiness, product lifecycle alignment, documentation, and vulnerability handling.
The CRA is a European Union regulation that establishes cybersecurity requirements for products with digital elements placed on the EU market. It covers areas such as secure development, vulnerability handling, technical documentation, user information, and lifecycle support.
Yes. The CRA applies to several products, including those with digital elements, and/or process digital data, and can connect directly or indirectly to another device or network. For many customers, that means the silicon platform, firmware, SDK, and supporting software ecosystem all matter in the overall compliance picture. For more information, visit Cyber Resilience Act - Questions and Answers.
Our current approach includes secure development lifecycle controls, risk and threat analysis, vulnerability handling, security testing, update management, and supporting documentation. For more information, see the Information Security Management System Overview.
Current references include PSA Certified Level 4 for Series 3 Secure Vault, ISO 27001:2022 certification, the public vulnerability disclosure policy and reporting channel, SBOM generation support in Simplicity Studio, Series 3 technical resources, product security pages, and public training content, including Tech Talks, Works With, webinars, and curriculum materials.
The main CRA obligations apply to products placed on the EU market from December 11, 2027, onward. However, there are earlier reporting obligations beginning on September 11, 2026. See the European Commission’s CRA summary for definitions of “placing on the market” and “making available on the market,” as well as the CRA application dates.
Vulnerability handling is a core part of the readiness story. Silicon Labs operates PSIRT processes and public vulnerability disclosure mechanisms, and we are maturing coordinated vulnerability handling, advisory generation, and reporting readiness to support the stricter operational timelines introduced by the CRA.
Silicon Labs currently provides SBOM generation capability in Simplicity Studio for supported projects. SBOMs are an important transparency mechanism under CRA-related discussions because they help identify software components and dependencies used in product builds.
Silicon Labs’ public Product Longevity Commitment and SDK Release and Maintenance Policy help customers understand baseline hardware lifecycle expectations, software maintenance timing, and where extended maintenance options may be available.
-
Training
Training
IoT Security Training: Works With 2022
Our IoT security training reviews regulations and trends and how you can keep all facets of your IoT devices secure, including hardware, software, and more.
IoT Security Sessions:
- SIOT-101: IoT Security Regulation and How it Drives Innovation
- SIOT-102: Regulations Will Demand Security Warranties in IoT Devices
- SIOT-104: Wireless Stack Integration with TrustZone and Secure Vault
- SIOT-201: Applying Security to Verify the Authenticity of IoT Products
- SIOT-203: Onboarding IoT Devices and Security Management
-
Services
Services
Custom Part Manufacturing Service (CPMS)
Customize Your Wireless Hardware and MCUs with Advanced Security and Unique Certificates.
Building an IoT device was easy in the past: developing code, flashing it on a chip, and manufacturing. Today, security is the ultimate challenge for IoT device makers. Your IoT device faces severe security threats throughout its entire supply chain, starting at the beginning of the outsourced manufacturing process.
CPMS for High-Volume Connected Devices
-
Resources
Resources
Featured IoT Security Resources
White Papers
Silicon Labs Blog
White Papers
White Papers
Silicon Labs Blog
Silicon Labs Blog
Silicon Labs Blog
-
Report Vulnerability
Report Vulnerability
Have you Discovered a Vulnerability?
Our Product Security Incident Response Team (PSIRT) is responsible for ensuring the vulnerabilities discovered in our products are mitigated and communicated responsibly. If you detect a security threat, let us know.
Information on how to subscribe to security notices can be found here.
Visit our FAQ page for more information on vulnerability reporting.
Bug Bounty Program
Coming Soon in 2026.
Submission Form
Please submit your bug via our Submission Page.
Thanks for helping keep Silicon Labs and our users safe!